Cybersecurity is crucial in today’s digital world, where data breaches and cyberattacks are becoming increasingly common.
Learning cybersecurity equips you with the skills and knowledge to protect yourself, your organization, and your clients from these threats.
You’ll gain a deeper understanding of how cybercriminals operate, learn to identify vulnerabilities, and develop strategies to mitigate risks.
A strong cybersecurity background can open doors to exciting careers in various industries, from tech giants to government agencies.
Finding the right cybersecurity course on Coursera can be challenging with so many options available.
You’re searching for a program that is comprehensive, engaging, and taught by experts, but also aligns with your learning style and goals.
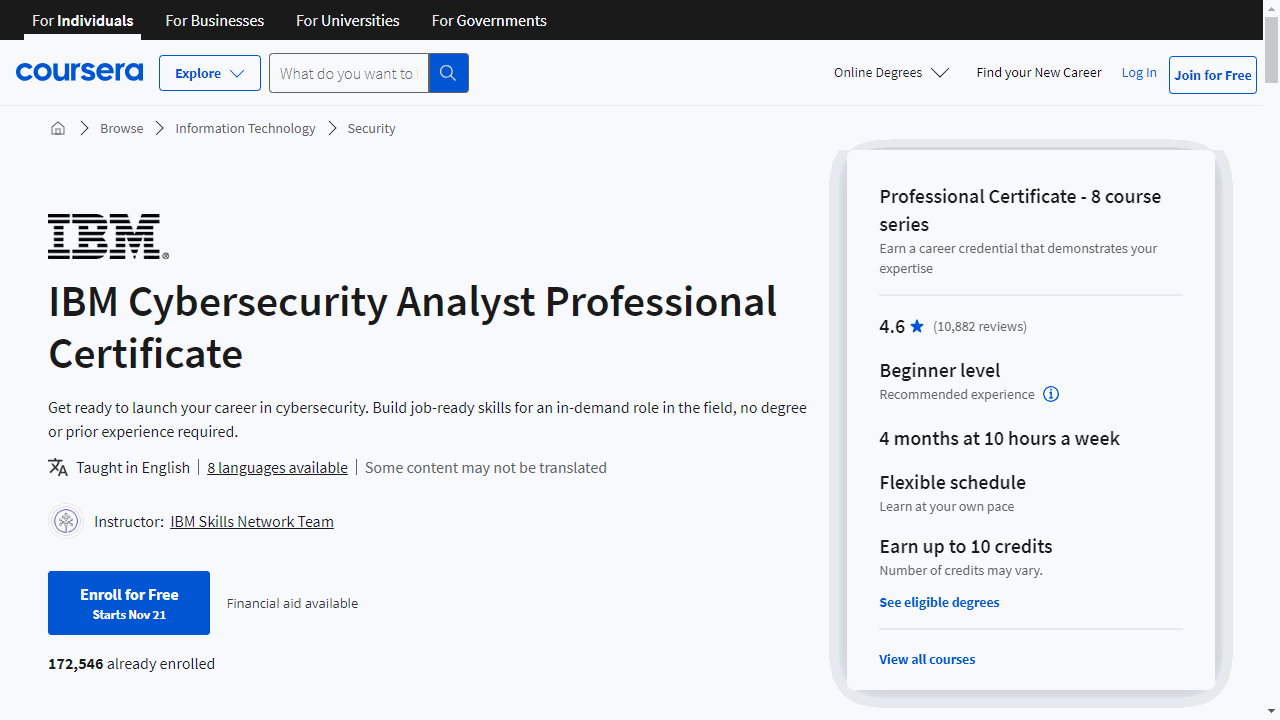
For the best cybersecurity course overall on Coursera, we recommend the IBM Cybersecurity Analyst Professional Certificate.
This program is a comprehensive eight-course series that covers a wide range of cybersecurity topics, from fundamental concepts to advanced techniques.
You’ll learn about common threats, security tools, incident response, compliance frameworks, and much more.
The program also includes practical exercises and case studies to solidify your understanding and prepare you for real-world challenges.
While this program is our top pick, there are other excellent cybersecurity courses available on Coursera.
Keep reading to discover more recommendations for beginners, intermediate learners, and experts, as well as courses focused on specific cybersecurity tools, techniques, and career paths.
Quick Picks
| Course Name | Skills Acquired | Enroll Now |
|---|---|---|
| IBM Cybersecurity Analyst Professional Certificate | • Understanding cyber threats and security concepts • Knowledge of cybersecurity roles and operating system security • Hands-on experience with penetration testing and incident response |
👉 Go To Course |
| IT Fundamentals for Cybersecurity Specialization | • Foundational cybersecurity knowledge and critical thinking • Understanding of cybersecurity roles, processes, and operating system security • Knowledge of cybersecurity compliance frameworks and system administration |
👉 Go To Course |
| Google Cybersecurity Professional Certificate | • Foundational knowledge of cybersecurity and its role in business • Understanding of security risks, networks, and tools like Linux and SQL • Hands-on experience with incident detection and response |
👉 Go To Course |
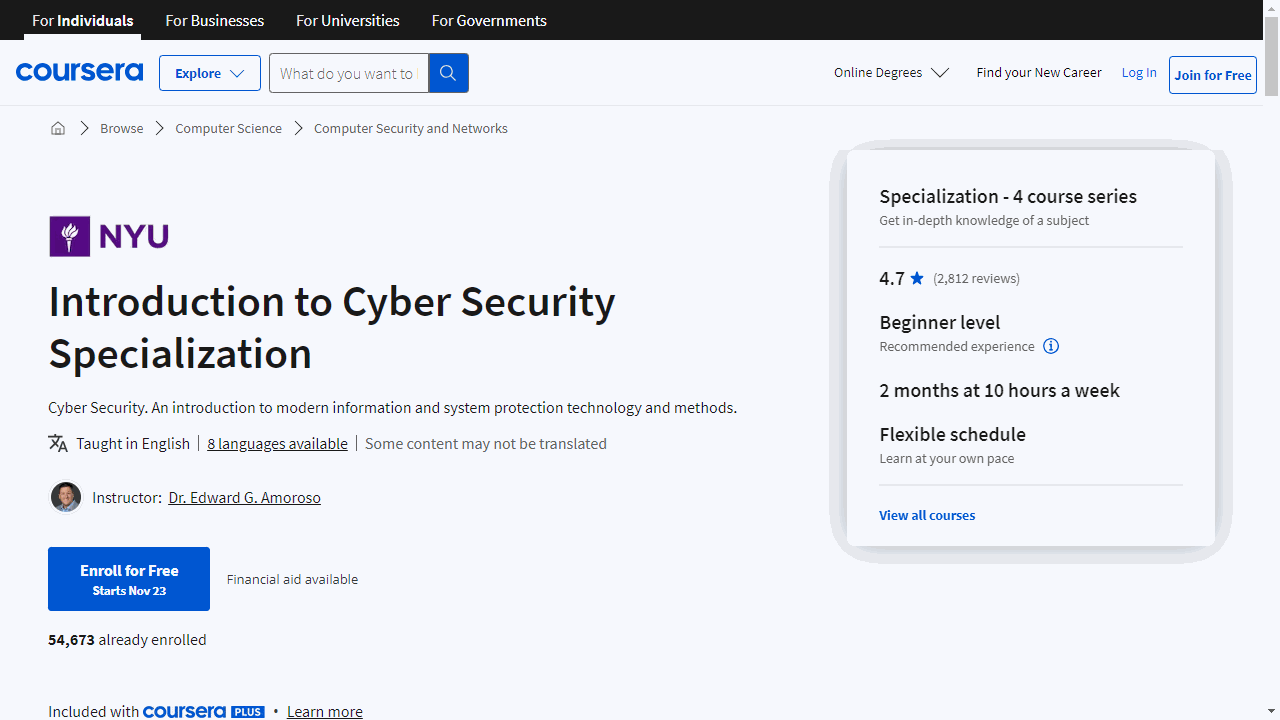
| Introduction to Cyber Security Specialization | • Understanding common cyber threats and applying the CIA framework • Knowledge of cyber attack countermeasures and authentication protocols • Skills in real-time cyber threat detection and mitigation |
👉 Go To Course |
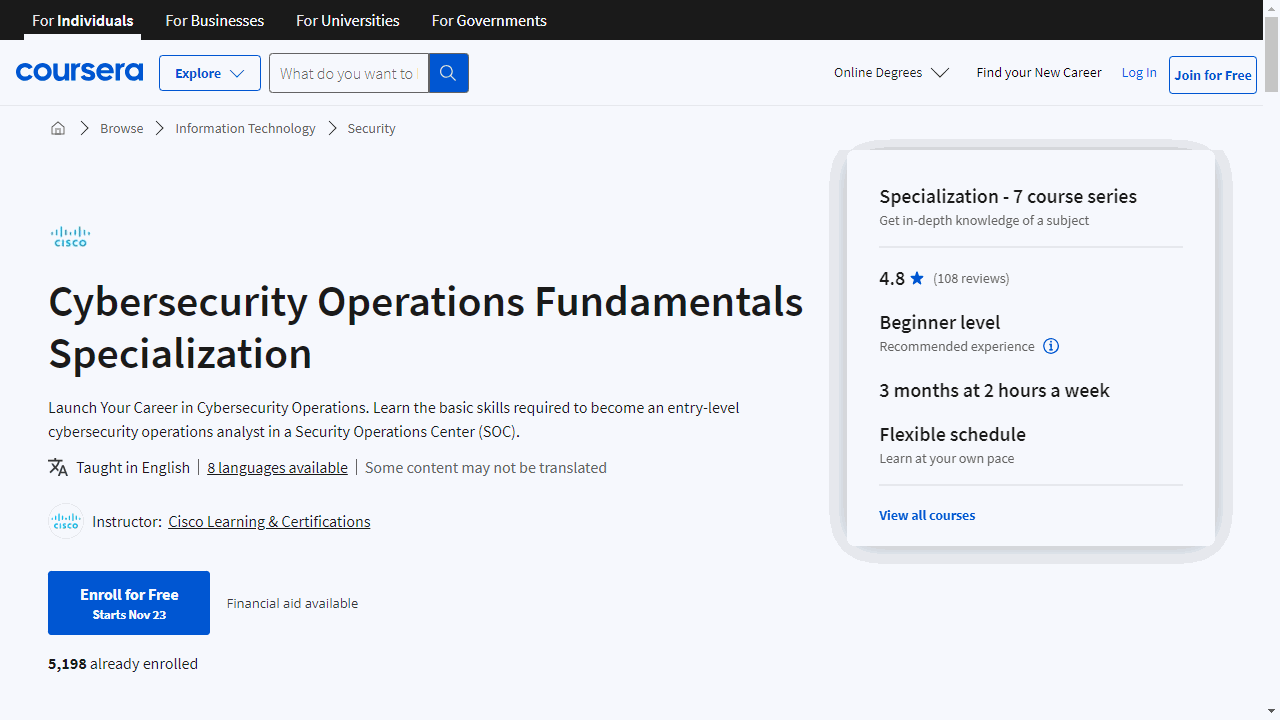
| Cybersecurity Operations Fundamentals Specialization | • Understanding SOC roles and responsibilities • Deep dive into Windows, Linux, and Mac OS security • Skills in network security monitoring and data security |
👉 Go To Course |
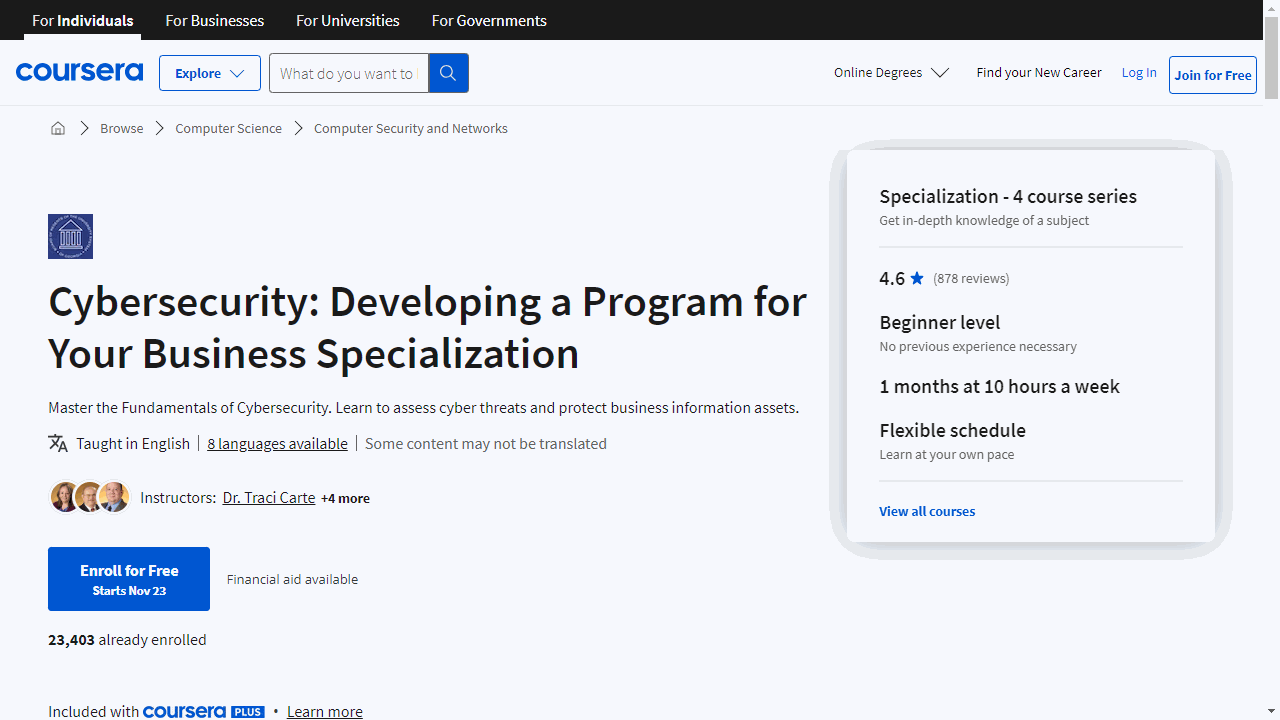
| Cybersecurity: Developing a Program for Your Business Specialization | • Understanding cybersecurity in the context of mobility and IoT • Addressing the human element in cybersecurity risk management • Developing and implementing cybersecurity programs for businesses |
👉 Go To Course |
IBM Cybersecurity Analyst Professional Certificate
Begin with “Introduction to Cybersecurity Tools & Cyber Attacks,” where you’ll grasp the evolution of cyber threats and familiarize yourself with fundamental security concepts and tools.
This course lays the groundwork for understanding the complexities of protecting digital assets.
Progress to “Cybersecurity Roles, Processes & Operating System Security,” which delves into the human aspect of cybersecurity.
You’ll explore various roles and their responsibilities, and gain practical knowledge of operating system commands.
Understanding virtualization’s impact on security is another key takeaway.
The “Cybersecurity Compliance Framework & System Administration” course is pivotal for those looking to navigate the maze of industry standards and compliance requirements.
It also covers the nuts and bolts of user and server administration, emphasizing the importance of endpoint security and the intricacies of cryptography.
Network security is the focus of the “Network Security & Database Vulnerabilities” course.
Here, you’ll dive into the technicalities of network infrastructure and learn how to identify and mitigate database vulnerabilities—a critical skill for safeguarding an organization’s data.
“Penetration Testing, Incident Response and Forensics” offers a hands-on approach to proactive security measures and reactive strategies.
You’ll explore the tools and techniques for penetration testing, learn to craft effective incident response plans, and understand the meticulous process of digital forensics.
In “Cyber Threat Intelligence,” the curriculum shifts to defensive strategies and the importance of threat intelligence.
You’ll learn to use tools for network monitoring and data protection, ensuring you’re well-versed in the latest defensive tactics.
The program culminates with the “Cybersecurity Capstone: Breach Response Case Studies,” where you apply your cumulative knowledge to real-world scenarios.
This practical exercise simulates the decision-making process in the aftermath of a cyber breach, preparing you for real-life challenges.
Completing the series with the “IBM Cybersecurity Analyst Assessment” solidifies your understanding and earns you the IBM Cybersecurity Analyst Professional Certificate, a testament to your readiness for a role in the field.
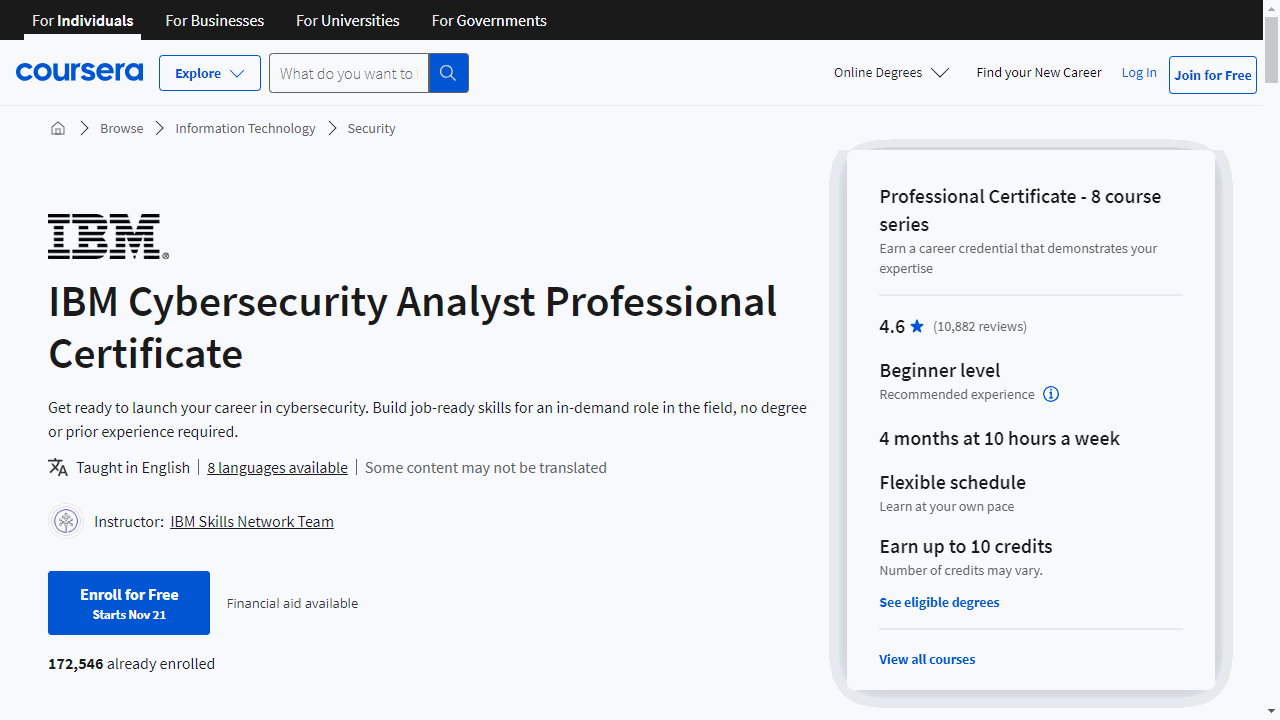
IT Fundamentals for Cybersecurity Specialization
This suite of courses is meticulously designed to build your cybersecurity expertise from the ground up.
The journey begins with “Introduction to Cybersecurity Tools & Cyber Attacks,” where you’ll delve into the evolution of cybersecurity, understand the motives behind cyber threats, and familiarize yourself with essential concepts and tools.
This course doesn’t just teach you the basics; it sharpens your critical thinking skills, which are vital in the cybersecurity realm.
Completing this course earns you an IBM digital badge, a valuable addition to your professional profile.
Next, “Cybersecurity Roles, Processes & Operating System Security” offers a closer look at the human and procedural aspects of cybersecurity.
You’ll explore various roles within an organization and the key processes that fortify its defenses.
The course also covers operating system security for Windows, Mac/OS, Linux, and Mobile, along with the concept of virtualization.
Another IBM digital badge awaits you upon completion, marking your growing expertise.
In “Cybersecurity Compliance Framework & System Administration,” you’ll tackle the critical topics of compliance and industry standards, such as NIST and GDPR.
The course equips you with practical skills in user and server administration, emphasizing the importance of patch management and endpoint security.
You’ll also dive into cryptography, learning how encryption protects company software.
Lastly, “Network Security & Database Vulnerabilities” rounds out your education with a focus on protecting an organization’s network infrastructure.
You’ll grasp the essentials of the TCP/IP and OSI models, and understand how to secure databases against common threats like SQL Injection.
This knowledge is crucial for identifying and mitigating network vulnerabilities.
Each course in this specialization is a stepping stone towards becoming a proficient Jr Cybersecurity Analyst.
The IBM digital badges you collect along the way not only validate your skills but also enhance your employability in the ever-evolving IT landscape.
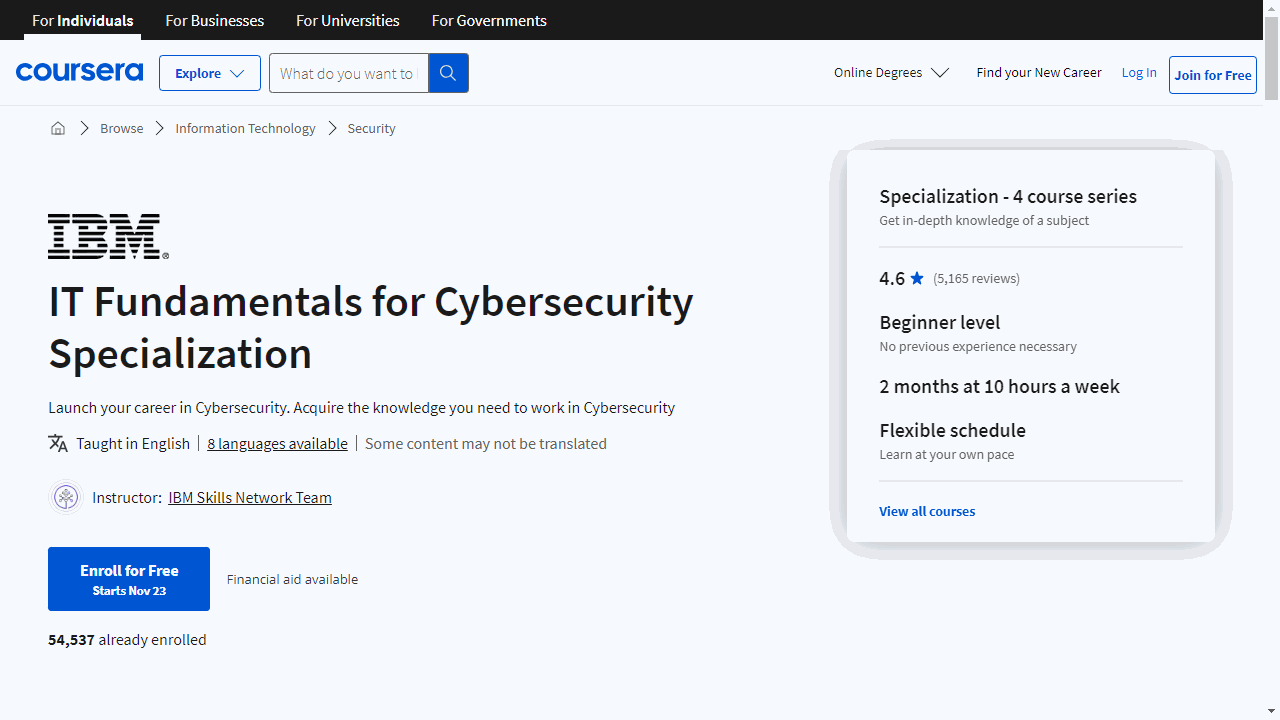
Google Cybersecurity Professional Certificate
This certificate is designed to equip you with the foundational skills necessary for an entry-level cybersecurity position, and it does so with a clear, structured approach.
The journey begins with “Foundations of Cybersecurity,” where you’ll gain an understanding of the field’s history and its significance in modern business.
You’ll explore the roles and essential skills of a cybersecurity analyst, guided by Google’s own experts.
The course also introduces you to the CISSP security domains and the tools commonly used in the industry.
Building on that foundation, “Play It Safe: Manage Security Risks” delves into risk management, teaching you about security frameworks and controls.
You’ll learn to conduct a security audit and respond to threats, arming you with practical knowledge of the NIST framework.
As you progress to “Connect and Protect: Networks and Network Security,” the focus shifts to the intricacies of networking.
Understanding how data travels and the importance of securing networks against attacks is crucial, and this course covers that, including the use of firewalls and VPNs.
“Tools of the Trade: Linux and SQL” hones in on technical skills.
You’ll get comfortable with the Linux command line and SQL database management—skills that are indispensable for cybersecurity professionals.
In “Assets, Threats, and Vulnerabilities,” the curriculum encourages you to adopt an attacker’s mindset to better defend against threats.
You’ll learn about encryption, authentication, and threat modeling, which are key to identifying and mitigating risks.
The sixth course, “Sound the Alarm: Detection and Response,” is where you’ll tackle incident detection and response.
You’ll get hands-on with tools like IDS and SIEM, learning to analyze network traffic and respond to security incidents effectively.
“Automate Cybersecurity Tasks with Python” introduces you to Python programming, demonstrating how automation can enhance security measures.
You’ll write scripts to streamline tasks, a skill that boosts efficiency and effectiveness.
Finally, “Put It to Work: Prepare for Cybersecurity Jobs” focuses on the soft skills and practical steps needed to secure a job.
From crafting a resume to acing an interview, this course prepares you to present your newfound skills to potential employers.
Throughout the certificate, Google’s cybersecurity professionals provide insights and mentorship, ensuring that the knowledge you gain is both current and applicable.
The courses are designed to be interactive and engaging, with a balance of theory and hands-on practice.
This certificate stands out for its accessibility; no prior experience is needed to start.
It’s a comprehensive program that covers a broad range of topics without overwhelming you.
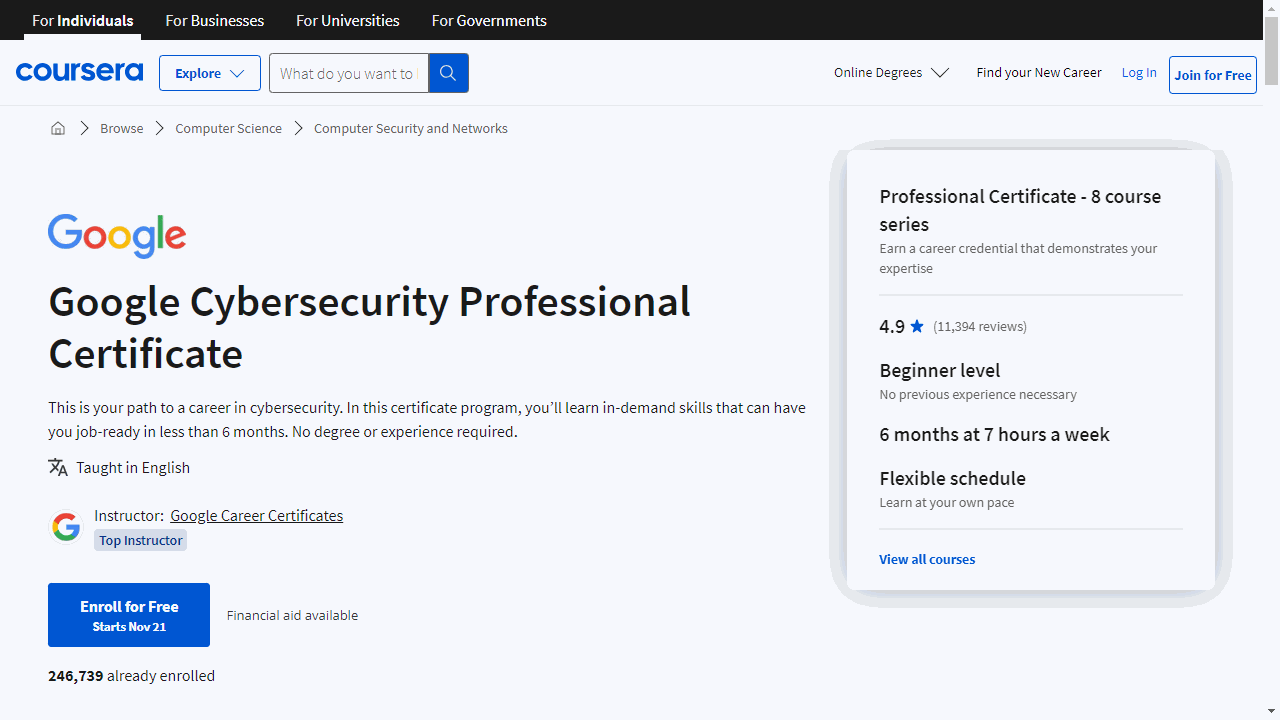
Introduction to Cyber Security Specialization
The journey begins with “Introduction to Cyber Attacks,” where you’ll gain a foundational understanding of common cyber threats.
This course demystifies complex cybersecurity concepts, from Unix kernel hacks to Internet worms, and teaches you to apply the CIA (confidentiality, integrity, availability) framework to real-world scenarios.
You’ll also learn to conduct basic cyber security risk analysis, prioritizing threats to safeguard assets effectively.
In “Cyber Attack Countermeasures,” the focus shifts to defense.
You’ll explore foundational models like Bell-LaPadula and delve into authentication protocols, including RSA SecureID and Kerberos.
The course simplifies cryptography, breaking down block ciphers and public-key systems, and introduces SSL schemes that underpin secure online transactions.
“Real-Time Cyber Threat Detection and Mitigation” sharpens your skills in network security.
You’ll understand TCP/IP protocol vulnerabilities and configure firewalls to thwart intrusions.
The course also addresses advanced persistent threats (APTs), offering strategies to protect enterprise environments from sophisticated attacks.
Finally, “Enterprise and Infrastructure Security” broadens your perspective with advanced topics relevant to modern enterprises.
You’ll navigate compliance frameworks such as NIST and PCI, understand the security implications of emerging technologies like blockchain and IoT, and learn about mobile and cloud security strategies.
This course also provides career planning advice, helping you stay competitive in the cybersecurity field.
Cybersecurity Operations Fundamentals Specialization
This specialization is designed to build a solid foundation in cybersecurity operations, making it ideal for associate-level cybersecurity analysts working in security operation centers.
The “Security Operations Center (SOC)” course is your entry point, focusing on the roles and responsibilities within a SOC.
You’ll learn about the adversaries, their tactics, and the strategic importance of SOCs in defending against cyber threats.
For those with a technical background, including knowledge of Cisco solutions, networking, and operating systems, “Endpoints and Systems” offers a deep dive into the intricacies of Windows, Linux, and Mac OS.
You’ll explore system architecture, processes, and administrative tasks, gaining practical skills for managing and securing endpoints.
In “Network Security,” the course shifts to the critical infrastructure of networks, introducing you to security monitoring tools and concepts like Access Control Lists and Network Address Translation.
This knowledge is vital for safeguarding the pathways through which data travels.
“Data Security” hones in on the types of data crucial for network security analytics.
You’ll become proficient in using SIEMs, understanding the Security Onion tool, and handling packet capture data, which is essential for incident investigation.
“Threat Analysis” teaches you to dissect cyber-attacks using models like the kill chain and diamond model.
This course empowers you to analyze and counteract threats effectively, enhancing your ability to protect your organization.
“Threat Investigation” elevates your skills in proactive threat hunting.
You’ll learn about the Common Vulnerability Scoring System and utilize threat intelligence to anticipate and neutralize emerging threats.
Finally, “Threat Response” rounds out the specialization by focusing on incident response.
You’ll learn to develop response plans, categorize incidents, and understand compliance regulations, ensuring you’re prepared to act decisively during security incidents.
Cybersecurity: Developing a Program for Your Business Specialization
The specialization starts with the “Cybersecurity and Mobility” course, which tackles the intersection of cybersecurity and mobile technology.
You’ll learn from industry experts about the evolving nature of threats as mobile devices become more prevalent.
By the end of this course, you’ll understand how to adapt traditional security measures to protect critical data in a mobile-centric world.
In “Cybersecurity and the Internet of Things,” you’ll explore the security implications of IoT.
This course demystifies the latest trends and provides insights into how interconnected devices can pose risks to business environments.
It’s a blend of technical knowledge and strategic planning, ensuring you’re prepared to address IoT-related security concerns.
Human behavior is often the most unpredictable element in cybersecurity, which is where “Cybersecurity and the X-Factor” comes in.
This course delves into the human aspect, offering strategies to mitigate risks posed by human error or malicious intent.
You’ll learn about the importance of Security Education, Training, and Awareness (SETA) programs and how to implement them effectively to raise cybersecurity awareness.
The capstone, “The Business of Cybersecurity Capstone,” ties everything together.
It focuses on information security management, covering governance, risk management, policy creation, and legal and ethical considerations.
This course is the culmination of the Specialization, cementing your understanding of how to integrate cybersecurity strategies into business operations.
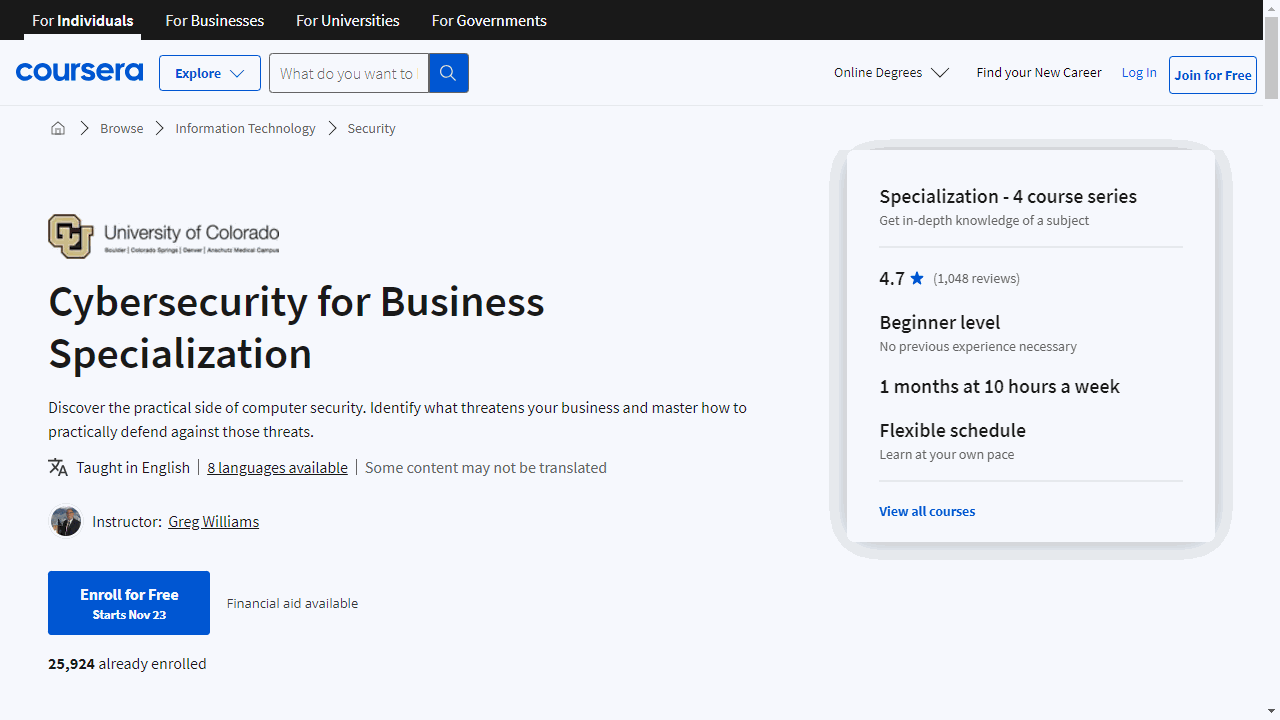
Cybersecurity for Business Specialization
The specialization kicks off with “Introduction to Cybersecurity for Business.”
This course lays the foundation, demystifying how security protects everything from your bank’s website to your own network.
You’ll gain insights into cybersecurity, information security (InfoSec), risk assessment, and attack surfaces—essential concepts for identifying your business’s vulnerabilities.
“Cyber Threats and Attack Vectors” takes you deeper into the cybersecurity arena.
It’s not just about recognizing the threats; it’s about understanding the mechanics of breaches and developing a keen eye for the signs of an attack.
This knowledge is crucial for preemptive defense strategies.
In “Detecting and Mitigating Cyber Threats and Attacks,” the focus shifts to action.
You’ll learn to detect potential breaches and implement mitigation strategies.
The course equips you with the tools to recommend security solutions and analyze past breaches to prevent future incidents.
Finally, “Proactive Computer Security” empowers you to actively test and refine your security measures.
Through penetration testing and setting up decoys, you’ll validate the effectiveness of your defenses, ensuring your business remains fortified against cyber threats.
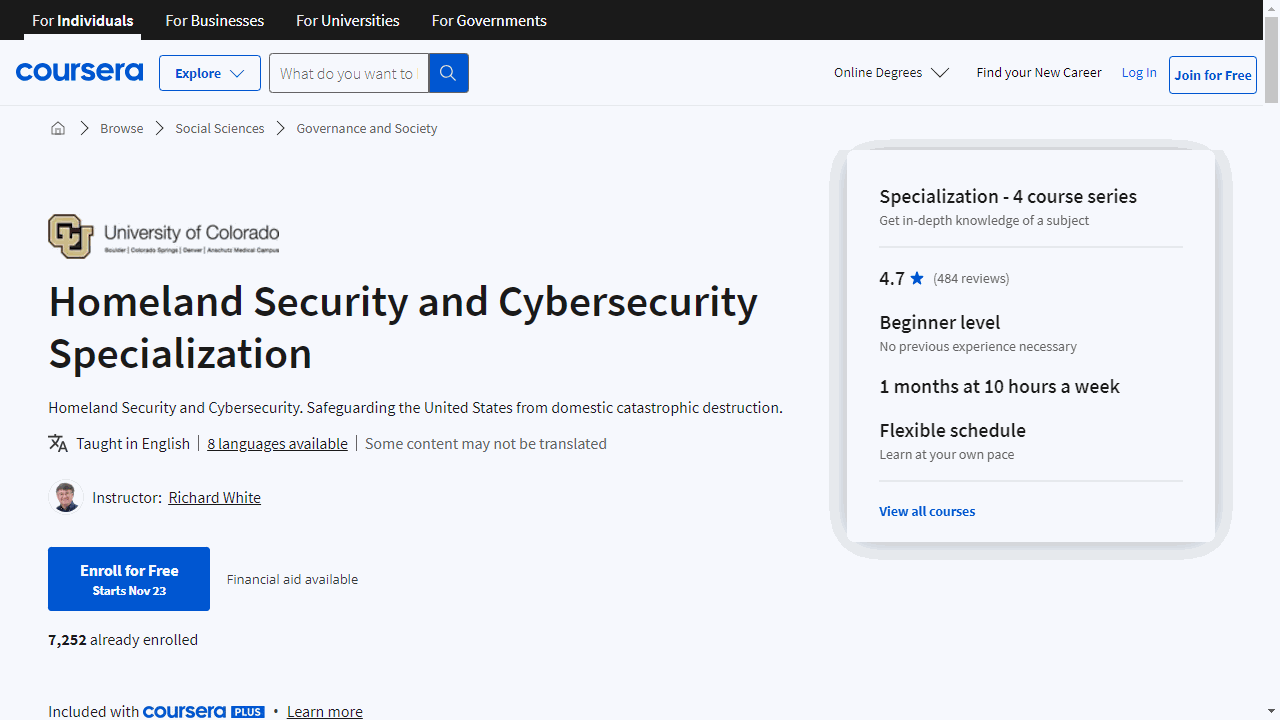
Homeland Security and Cybersecurity Specialization
The first course, “Homeland Security & Cybersecurity Connection - It’s Not About the Terrorists,” grounds you in the critical relationship between national safety and cybersecurity.
You’ll explore the evolution of threats and the importance of digital defense mechanisms in a world where technology can be both a tool and a weapon.
Moving on, “Cybersecurity Policy for Water and Electricity Infrastructures” zeroes in on the policies safeguarding our essential services.
You’ll delve into the Risk Management Framework and learn how the NIST Cybersecurity Framework is applied to protect these vital sectors from cyber threats.
This course emphasizes the importance of securing the systems we rely on daily.
In “Cybersecurity Policy for Aviation and Internet Infrastructures,” the focus shifts to the sectors that keep us connected and mobile.
You’ll examine the cybersecurity measures that keep our skies safe and our online presence secure, through the lens of the Transportation Roadmap and the Cyber Assessment Risk Management Approach.
Lastly, “Homeland Security & Cybersecurity Future” offers a forward-looking perspective, discussing emerging technologies and strategies to mitigate cyber risks.
It also provides insights into the cybersecurity profession for those considering it as a career.
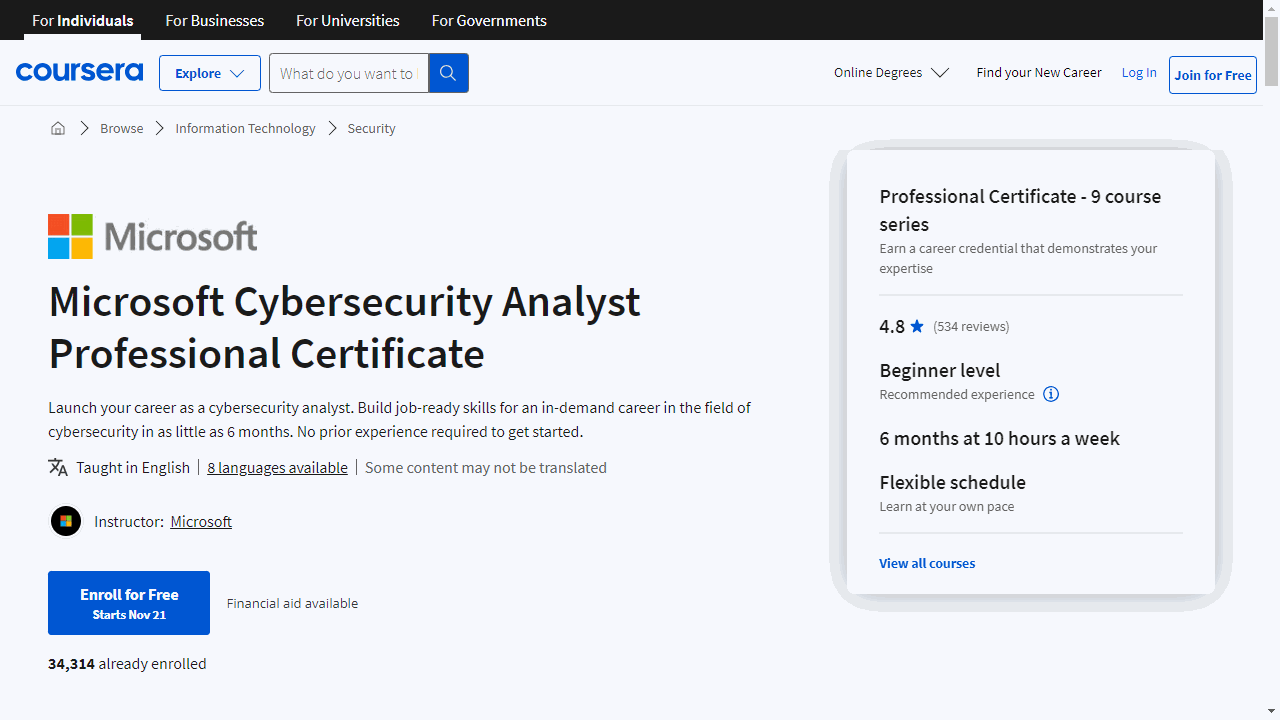
Microsoft Cybersecurity Analyst Professional Certificate
Beginning with “Introduction to Computers and Operating Systems and Security,” you’ll learn to identify computer components, understand their interaction with operating systems, and get a primer on the cybersecurity landscape.
This course isn’t just informative; it’s a practical step towards the Microsoft SC-900 exam and the subsequent certification.
Moving on, “Introduction to Networking and Cloud Computing” expands your expertise into the realms of network infrastructure and cloud services.
You’ll learn to set up, monitor, and secure networks, as well as navigate cloud computing environments.
This knowledge is crucial for today’s tech-driven workplaces and also preps you for the SC-900 exam.
With cyber threats constantly evolving, “Cybersecurity Threat Vectors and Mitigation” equips you to identify and counteract them.
You’ll delve into encryption techniques and compliance concepts, becoming well-versed in the strategies to safeguard digital assets.
Authentication and authorization are at the heart of cybersecurity, and “Cybersecurity Identity and Access Solutions using Azure AD” covers these topics thoroughly.
You’ll explore Azure Active Directory and its role in managing enterprise security, preparing you to implement robust access management policies.
In “Cybersecurity Solutions and Microsoft Defender,” you’ll learn to deploy cloud security policies and utilize tools like Microsoft Defender to protect against sophisticated threats.
This course emphasizes practical skills for defending Azure resources and understanding security standards.
“Cybersecurity Tools and Technologies” introduces you to the hands-on aspect of cybersecurity.
You’ll practice penetration testing and learn to interpret security scans, gaining skills that are directly applicable to securing cloud platforms.
If you are interested in the strategic side of cybersecurity, “Cybersecurity Management and Compliance” offers insights into data and record management, policy formation, and regulatory compliance.
You’ll also learn about Microsoft’s privacy principles and compliance management tools.
The program culminates with “Advanced Cybersecurity Concepts and Capstone Project,” where you apply your cumulative knowledge to threat modeling, secure development, and IoT security.
The capstone project is a chance to demonstrate your skills in a comprehensive security mitigation strategy plan.
To ensure you’re exam-ready, “Microsoft SC-900 Exam Preparation and Practice” provides a series of practice exams and study strategies.
This course is designed to boost your confidence and help you achieve certification.
Each course in this certificate program is crafted to be accessible, with no prior degree or experience required.
The learning is self-paced, allowing you to fit it into your schedule.
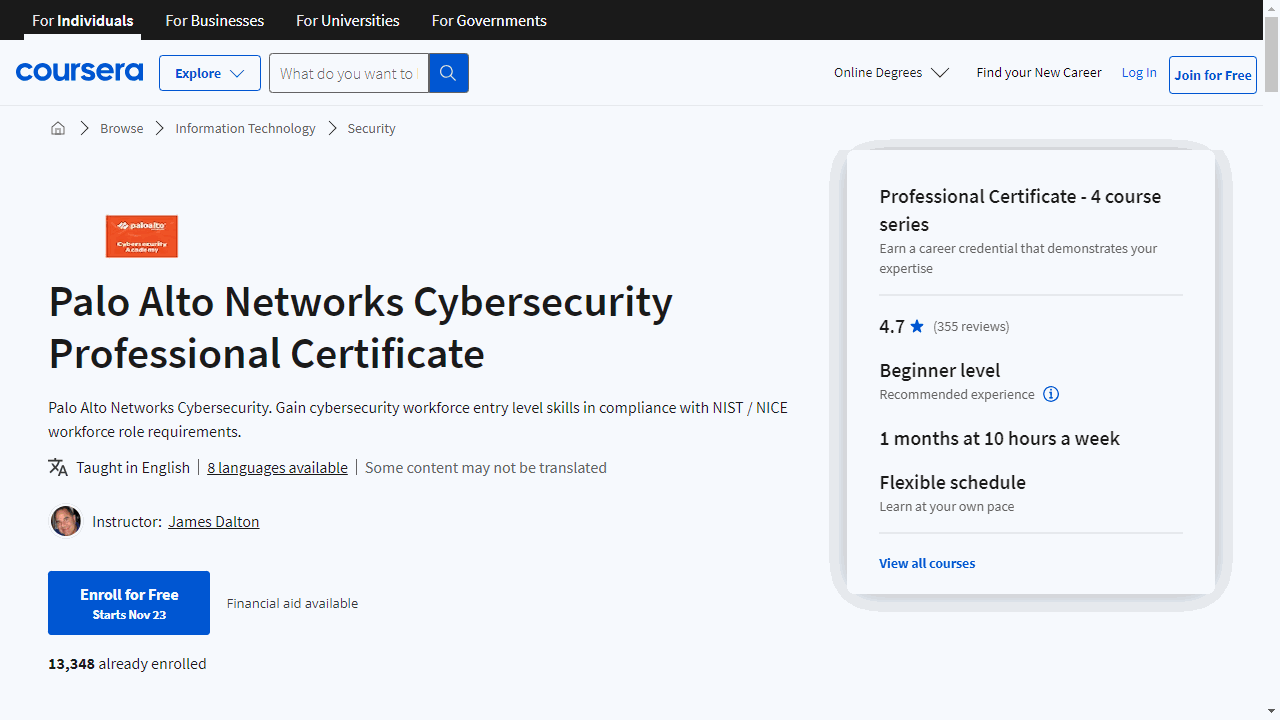
Palo Alto Networks Cybersecurity Professional Certificate
Begin with the “Palo Alto Networks Cybersecurity Foundation” course, where you’ll grasp the essentials of the cybersecurity field.
You’ll learn to identify and mitigate network threats, configure security zones, and implement policies on next-generation firewalls.
This course equips you with the knowledge to tackle modern computing challenges, understand attacker tactics, and secure enterprise networks.
The “Palo Alto Networks Network Security Fundamentals” course deepens your understanding by focusing on the principles of maintaining a secure network.
You’ll emerge with the ability to describe security concepts and apply basic configuration techniques, ensuring you can both conceptualize and apply network defenses.
In the “Palo Alto Networks Cloud Security Fundamentals” course, you’ll navigate the complexities of cloud security.
You’ll learn to protect cloud and SaaS applications, set up secure containers, and conduct vulnerability assessments in cloud environments.
This course is crucial for mastering the protection of data in the cloud, a skill highly sought after in today’s tech-driven market.
Finally, the “Palo Alto Networks Security Operations Fundamentals” course introduces you to SecOps, the proactive arm of cybersecurity.
You’ll explore how to collect intelligence, analyze threats, and leverage automation to respond to incidents efficiently.
This course is about enhancing your ability to protect digital assets in real-time.
Each course is designed to build on the last, culminating in a well-rounded skill set that includes authentication, cryptography, and cloud computing security.
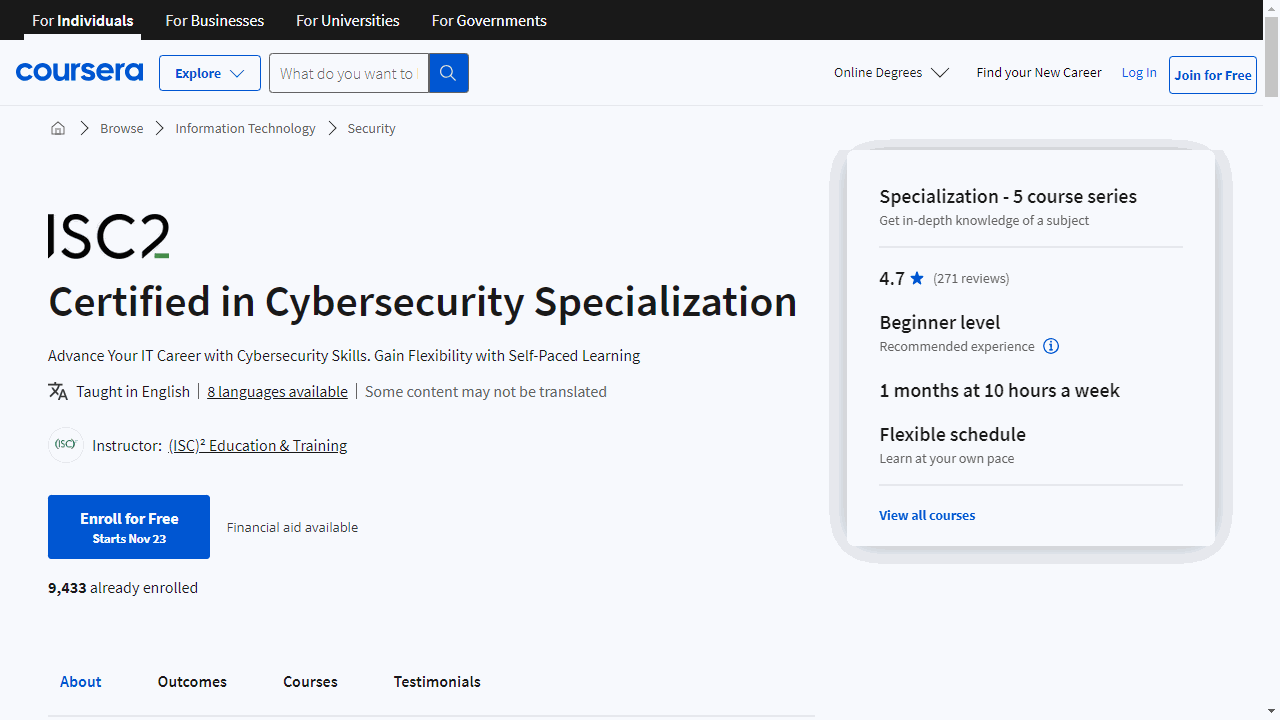
Certified in Cybersecurity Specialization
The journey begins with “Security Principles,” where you’ll grasp the core concepts of cybersecurity.
This course lays the groundwork, introducing you to risk management, security controls, and the ethical considerations outlined by the (ISC)2 Code of Ethics.
It’s practical knowledge that applies to both professional and personal digital security practices.
Moving on to “Incident Response, BC, and DR Concepts,” you’ll learn how to keep operations resilient against disruptions.
This course demystifies the strategies behind incident response, business continuity, and disaster recovery, teaching you how to craft plans that ensure an organization’s swift recovery from unforeseen events.
“Access Control Concepts” dives into the specifics of managing who can access what within an organization.
It’s a detailed look at physical and logical controls, emphasizing the importance of stringent access management to safeguard sensitive information.
In “Network Security,” the focus shifts to the backbone of the internet—networks.
You’ll explore how to identify and thwart cyber threats, ensuring the integrity and safety of networked systems.
This course is crucial for understanding the battleground where much of cybersecurity warfare takes place.
Lastly, “Security Operations” centers on the active defense of data and systems.
It covers data security, encryption, and the implementation of security policies.
This course is about fostering a security-first mindset, crucial for anyone responsible for protecting digital assets.
Designed for accessibility, this specialization requires no prior IT or cybersecurity experience, making it ideal for anyone eager to enter or advance in the field.
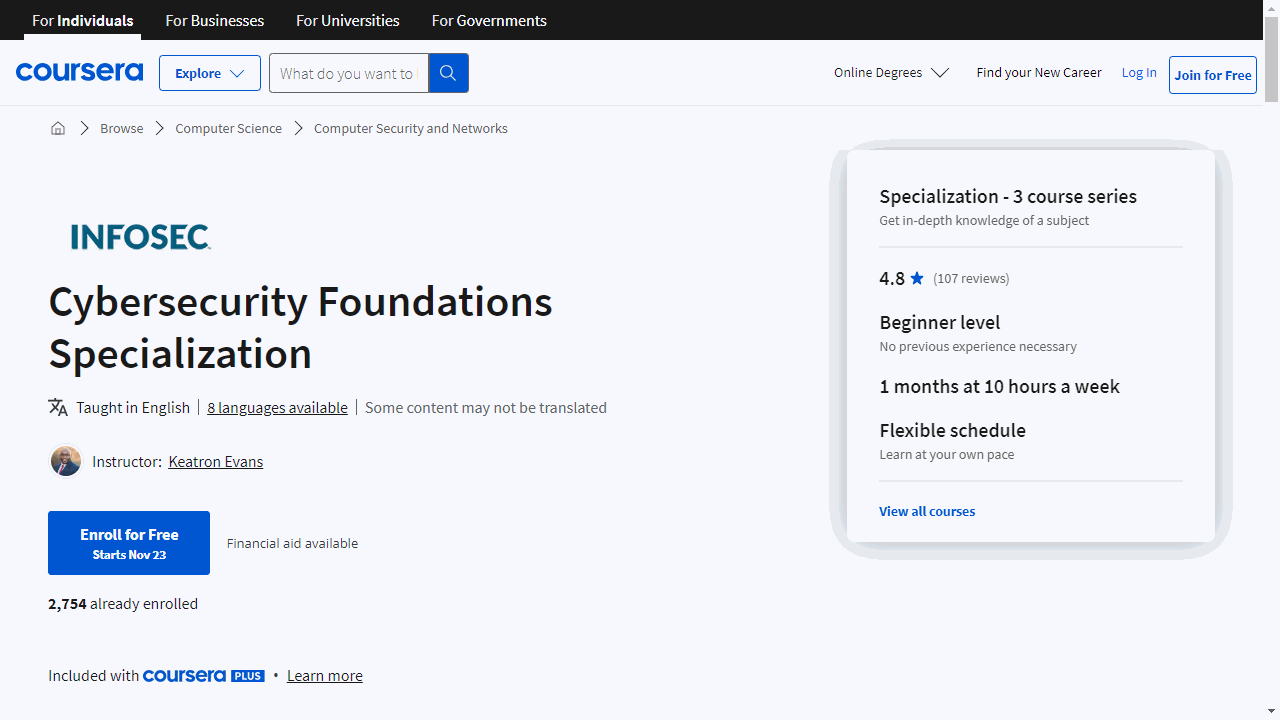
Cybersecurity Foundations Specialization
The specialization kicks off with “Introduction to Cybersecurity Foundations,” a course designed for true beginners.
You’ll grasp the essentials of cybersecurity, understand operating systems, and get a handle on risk management, all without prior technical experience.
Moving on, “Operating System Foundations” demystifies the core of your computer’s functionality.
You’ll compare Windows, Linux, and MacOS, gaining clarity on their differences and development.
This course is about making sense of the systems you interact with daily.
Lastly, “Cybersecurity Policy Foundations” takes you beyond the command line into the world of cybersecurity policies and frameworks.
It’s crucial for maintaining order in the digital realm, and you’ll learn how these guidelines shape a secure online environment.
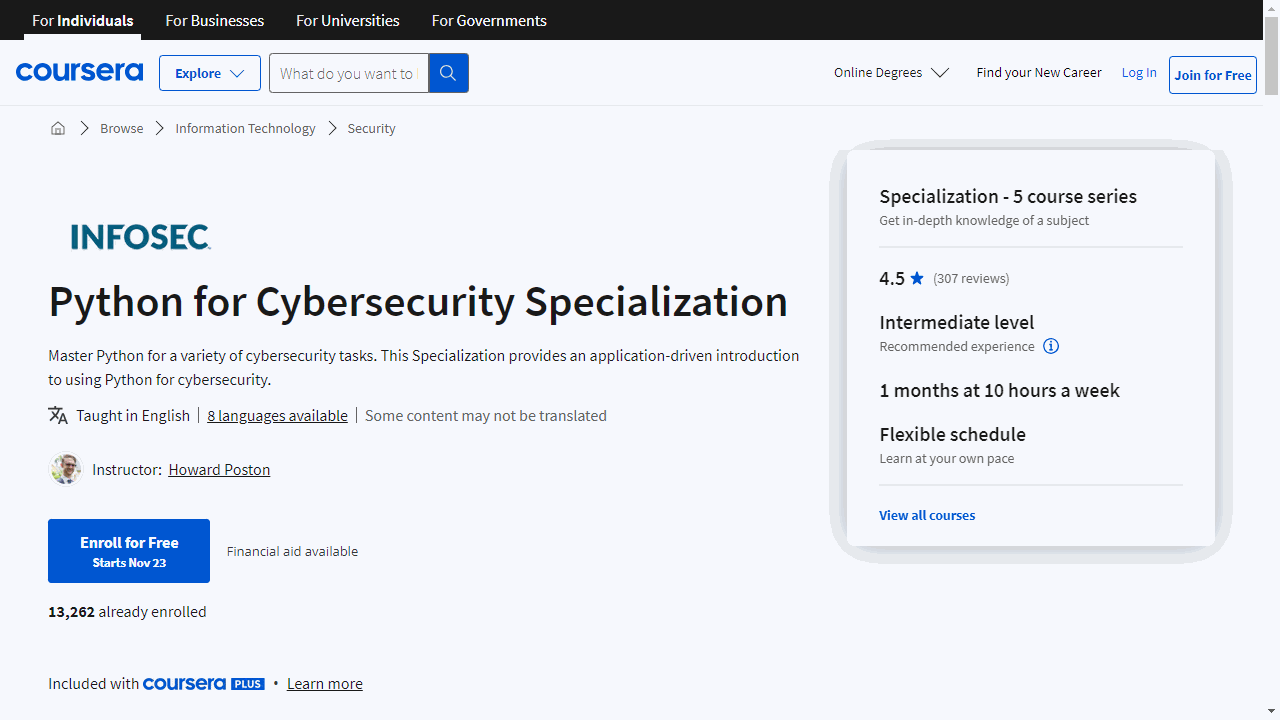
Python for Cybersecurity Specialization
If you want a cybersecurity specialization that focuses on Python, this is the one for you.
Kick off with “Introduction to Python for Cybersecurity,” where you’ll grasp the basics of Python in the context of cyber defense.
This course sets a strong foundation, emphasizing Python’s role in cybersecurity, without overwhelming you with unnecessary details.
Next, “Execution, Persistence, Privilege Escalation and Evasion” dives deeper.
You’ll explore how attackers operate and how Python can be used to disrupt these activities.
It’s a practical approach to understanding and combating common cyber attack strategies.
In “Credential Access, Discovery, Lateral Movement & Collection,” the focus shifts to the techniques used by cybercriminals to infiltrate networks.
You’ll learn to use Python to detect and mitigate such threats, enhancing your defensive strategies.
“Python for Command-and-Control, Exfiltration and Impact” covers the critical aspects of incident response and data protection.
You’ll gain insights into how Python can be employed to manage cyber incidents and safeguard information.
Finally, “Python for Active Defense” teaches proactive defense strategies.
This course empowers you to use Python to set up defenses that not only protect but also actively engage with threats to neutralize them before they escalate.
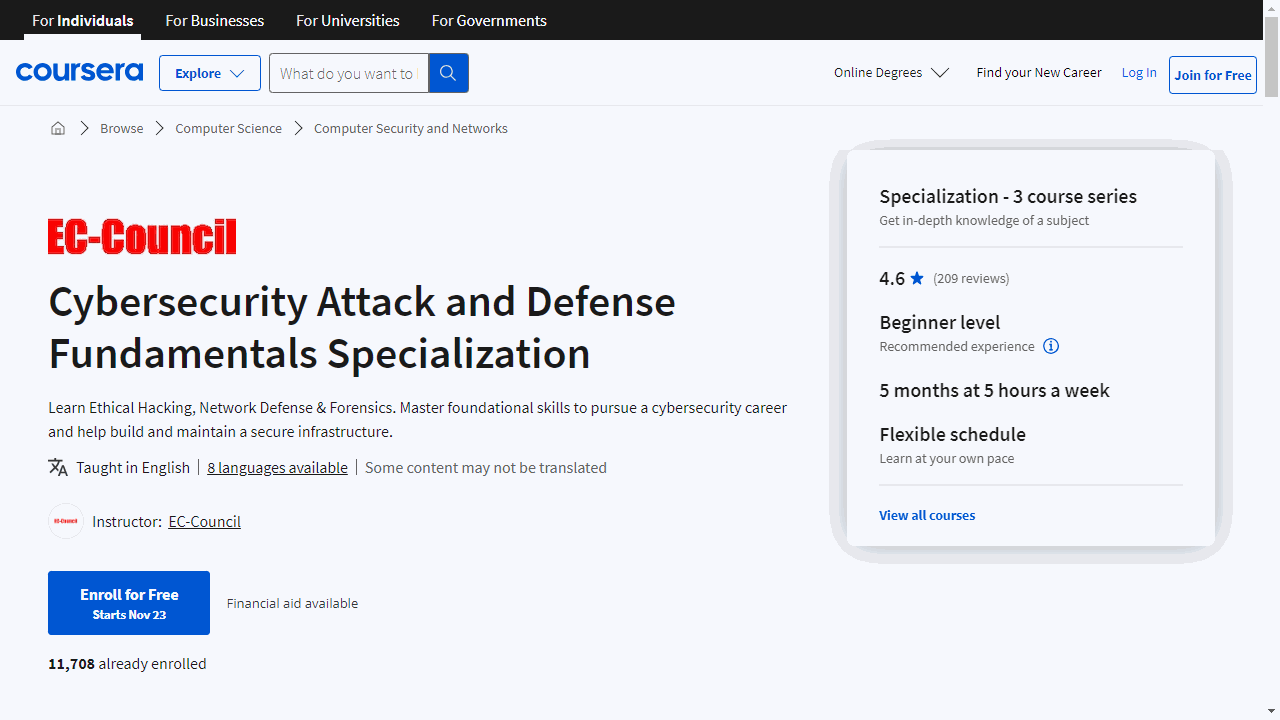
Cybersecurity Attack and Defense Fundamentals Specialization
Starting with “Ethical Hacking Essentials” (EHE), you’ll delve into the core of ethical hacking, learning to identify and address security vulnerabilities.
This course covers everything from password cracking to cloud computing, with practical labs to solidify your understanding.
Achieving EHE certification not only boosts your skillset but also enhances your resume, signaling to employers your readiness for the field.
Moving on to “Network Defense Essentials” (NDE), you’ll focus on safeguarding information systems.
This course emphasizes the importance of network security, from encryption to access control, and includes interactive labs for hands-on learning.
With an NDE certification, you demonstrate a comprehensive grasp of network defense strategies, making you an asset to any cybersecurity team.
Lastly, “Digital Forensics Essentials” (DFE) immerses you in the investigative side of cybersecurity.
You’ll explore techniques for uncovering and analyzing digital evidence, tackling topics like dark web forensics and malware analysis.
The DFE certification is proof of your ability to navigate complex digital investigations, a skill highly valued in the cybersecurity industry.
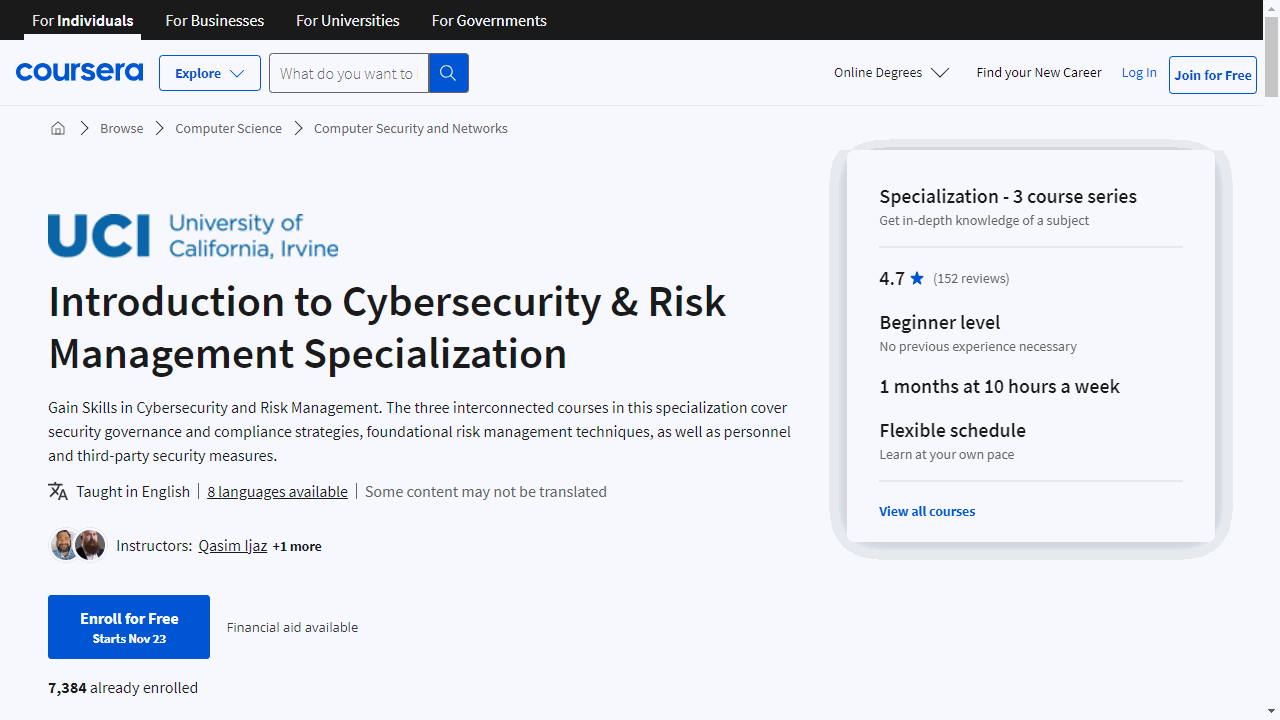
Introduction to Cybersecurity & Risk Management Specialization
The course “Security Governance & Compliance” is your entry point into cybersecurity.
It covers the core principles, such as the CIA triad, which stands for Confidentiality, Integrity, and Availability.
You’ll learn how to craft robust security governance frameworks, guided by the NIST cybersecurity framework, and gain an understanding of the critical laws and regulations that govern the cyber landscape.
This course is about setting the stage for a secure organizational environment through well-defined policies and strategies.
Moving on, “Introduction to Risk Management” sharpens your ability to identify and mitigate potential security threats.
It’s a deep dive into the relationship between assets, vulnerabilities, threats, and risks.
The course uses current case studies to bring theories to life, ensuring you can apply threat modeling and business continuity planning to real-world scenarios.
These skills are vital for maintaining operational resilience against cyber threats.
Lastly, “Personnel & Third-Party Security” focuses on the human aspect of cybersecurity.
It teaches you how to implement effective education and cybersecurity training programs, crucial for reinforcing an organization’s defense against cyber attacks.
You’ll also master Vendor Risk Management (VRM), learning to navigate the entire lifecycle of third-party relationships, from due diligence to termination.
Practical assignments give you a chance to apply these concepts, preparing you to manage the risks associated with both internal and external stakeholders.
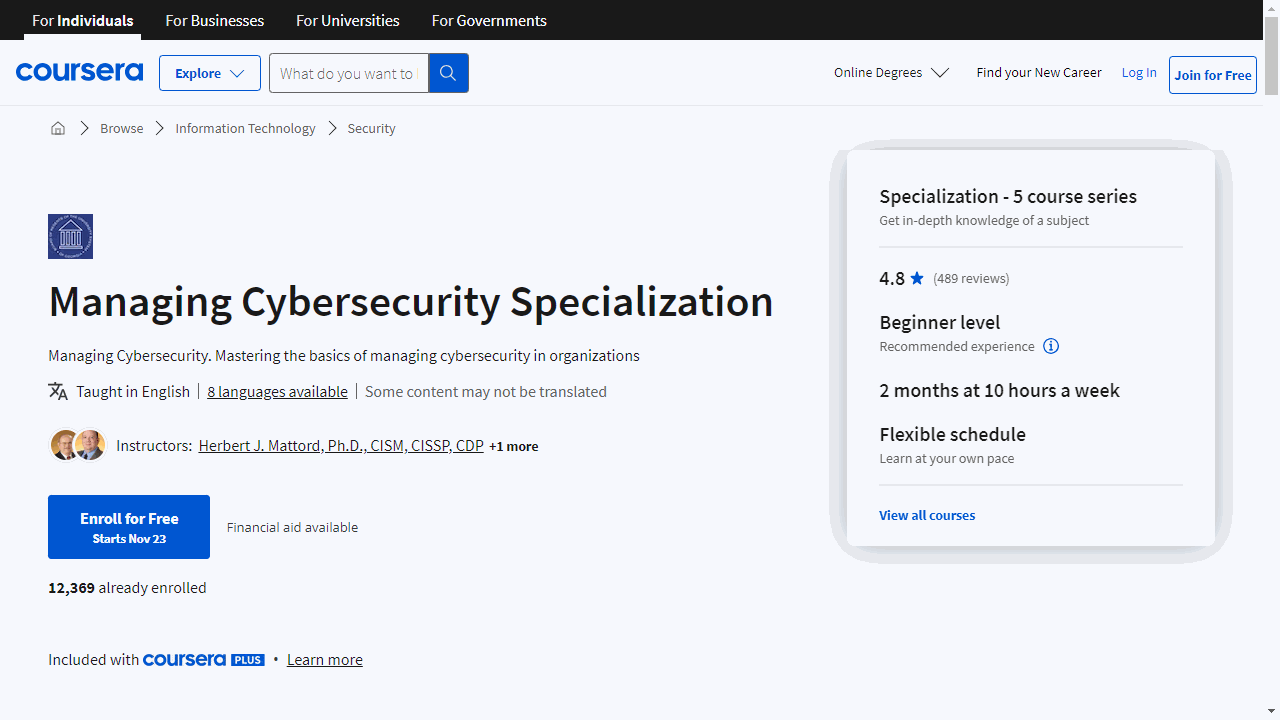
Managing Cybersecurity Specialization
The journey begins with “The Foundations of Cybersecurity,” where you’ll grasp the essential concepts and terminology, recognize threats, and learn to fortify digital assets against potential breaches.
Progressing to “The GRC Approach to Managing Cybersecurity,” you’ll delve into the critical roles of Governance, Risk Management, and Compliance.
This course empowers you with best practices in risk assessment and treatment, ensuring you’re adept at safeguarding information with strategic planning and robust policies.
In “Managing Network Security,” the focus shifts to the intricacies of protecting data across networks.
You’ll explore effective security measures, from identifying vulnerabilities to implementing advanced tools and methodologies that keep your network impermeable to intrusions.
The course “Managing Cybersecurity Incidents and Disasters” prepares you for the unexpected, providing strategies for incident response and disaster recovery.
You’ll learn to create contingency plans that ensure resilience and continuity in the face of cyber incidents or disasters.
Finally, “Road to the CISO – Culminating Project Course” charts the path from entry-level to the pinnacle of cybersecurity leadership.
It outlines the competencies and strategic insight required for the CISO role, emphasizing governance and the oversight of comprehensive cybersecurity programs.
This specialization is a concrete step towards mastering cybersecurity management.
It’s designed for practical application, with a focus on real-world tools, strategies, and skills such as risk management, business continuity, and cybersecurity governance.
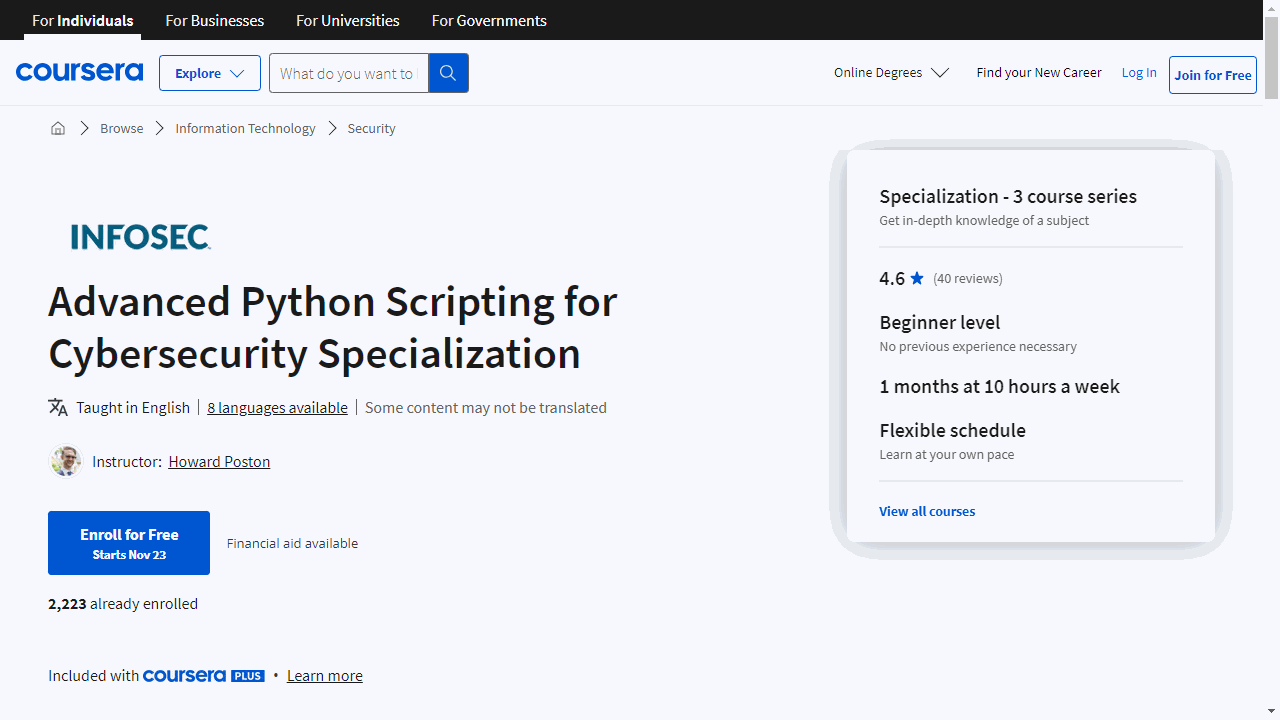
Advanced Python Scripting for Cybersecurity Specialization
Starting with the first course, “Advanced Python - Reconnaissance,” the specialization teaches you to automate reconnaissance tasks.
You’ll learn to script your way through gathering intelligence on target systems and executing password attacks to gain access.
It’s a practical approach to understanding the initial phase of cybersecurity operations.
Next, “Establishing Command-and-Control and Finding Credentials” takes you deeper into the attacker’s playbook.
You’ll master the creation of command-and-control channels using Python, allowing for discreet communication with compromised systems.
Additionally, you’ll acquire techniques for extracting sensitive information, including user credentials.
Finally, “Defensive Python” shifts your focus to defense, where you’ll apply Python for network analysis.
This course empowers you to detect and disrupt unauthorized connections, effectively safeguarding networks from potential threats.
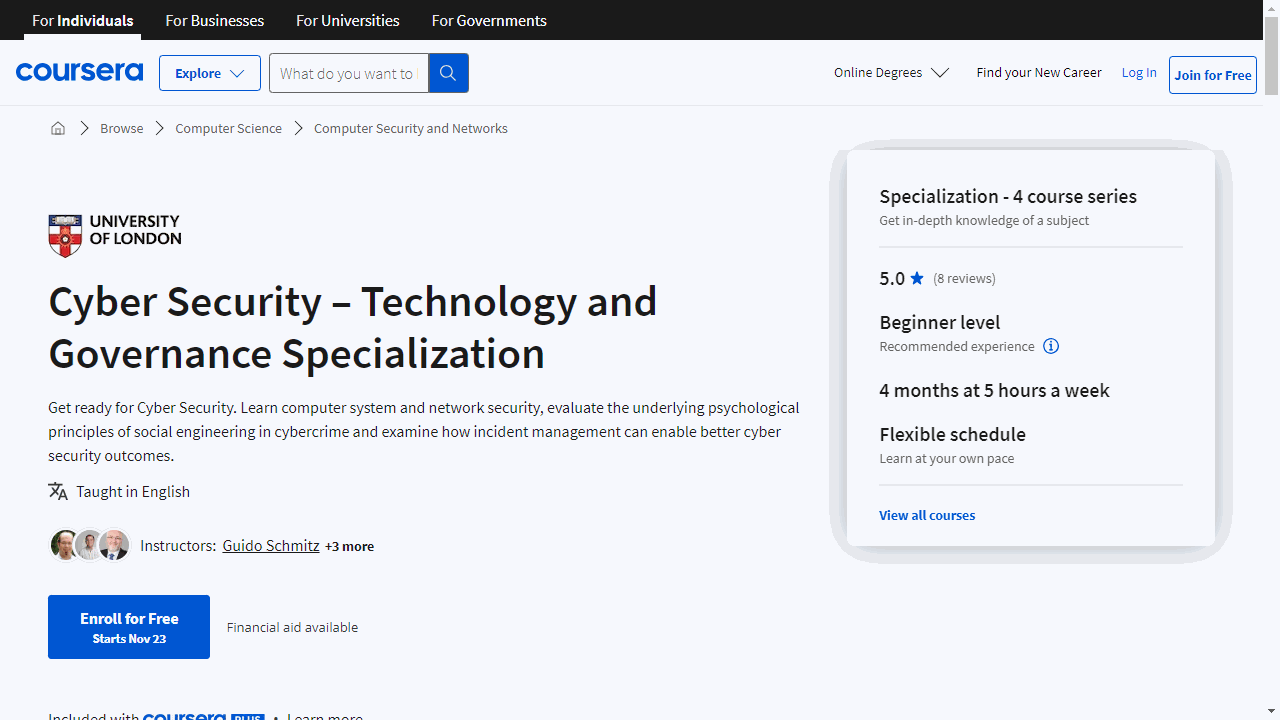
Cyber Security – Technology and Governance Specialization
The specialization kicks off with “Introduction to Computer Security,” a course that lays the groundwork without overwhelming you with technical jargon.
It’s a four-module journey through the essentials of computer systems, touching on hardware, applications, and basic security principles.
The interactive labs, including a Linux exploration and network protocol analysis with Wireshark, provide a practical foundation.
The second course, “Introduction to Network Security,” delves into the infrastructure that powers our digital world.
You’ll unravel the complexities of network protocols and learn to identify vulnerabilities.
By understanding the OSI model and TCP/IP stack, you’ll be equipped to anticipate and counteract network threats, a skill set in high demand across industries.
In “Security Management and Governance,” the focus shifts to the human element of cybersecurity.
You’ll navigate incident response, foster cyber resilience, and cultivate a security-conscious culture within organizations.
This course emphasizes the importance of leadership and strategic planning in protecting digital assets.
Finally, “Cybercrime” offers a deep dive into the psychology and mechanics of online crime.
You’ll dissect cybercrime definitions, actor motivations, and the impact of social engineering.
This course empowers you to critically analyze cybercrime reports and understand the human factors at play, rounding out your cybersecurity expertise.
Also check our posts on: